Train employees to recognize phishing attacks to avoid clicking on malicious links. Your confidential corporate information is secured because your employees are simply prevented from visiting sites that misuse such information. 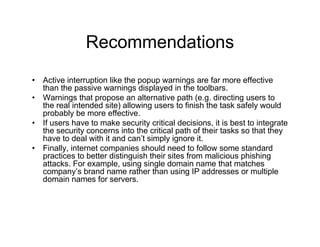 7 Best Ways to Prevent Fraud Before Its Too Late, Data Privacy And Protection: 11 Ways To Protect User Data, How To Easily Migrate Your Office 365 Tenant To A New One With The Same Domain, Cyber Security News Update Week 25 of 2022, What Is Dkim And Why You Should Use It To Secure Your Email, 5965 Village Way Suite 105-234 San Diego, CA 92130
7 Best Ways to Prevent Fraud Before Its Too Late, Data Privacy And Protection: 11 Ways To Protect User Data, How To Easily Migrate Your Office 365 Tenant To A New One With The Same Domain, Cyber Security News Update Week 25 of 2022, What Is Dkim And Why You Should Use It To Secure Your Email, 5965 Village Way Suite 105-234 San Diego, CA 92130
The information should be used to develop a decisioning score as to how likely those elements are to be representative of a malicious website. The one mistake companies make that leads them to fall victim to phishing attacks is Companies fall prey to phishing attacks because of careless and naive internet browsing. He has been employed in the healthcare industry since 1991, when he began working with Patient Care Technologies, an electronic medical record solutions provider. Privacy Policy But now, they know a bit more about our organization. You should have the ability to access logs to understand your threat environment. phishing poster security education educational figure awareness risk educause data A big component of protecting against phishing is employee training that actually works. Start by including definitions of spear phishing, ransomware, social engineering, CEO fraud, business email compromise, smishing and vishing.
If youre budget limited and can only afford to do one thing, then prevention technology should come first. Most phishing attacks will come in the form of an email, although they can also come by websites, physical mail or by phone calls. Second, if an employee is using the same password for multiple company accounts, then the hacker has now gained access to a great deal of confidential company data. There are several different reasons that businesses become victims of phishing attacks Three of the most popular being: inadequate security training, a lack of security policies, and a lack of proper social media usage. On the second front, one can secure the company by using SSO tools such as LastPass and Yubikey.
For businesses to effectively combat phishing they should be sure to include the following elements in a comprehensive cybersecurity policy: Every organization must have an acceptable use policy (AUP) that every new employee agrees to and signs as part of the onboarding process. Protecting against the phishing threat requires a comprehensive anti-phishing strategy. If, however, a senior administrator falls victim to the same attack, the malware could leverage domain account privileges to affect servers, endpoints, and sensitive data from across the entire network. So, to prevent this sort of phishing or at least to not make it so easy for the scammers, we recommend that companies disable the display of friendly names and contact images in their email clients. That's why we have strong cryptography today - the surviving algorithms have all been peer and public reviewed, attacked, and strengthened.  Dave Jevans is Marble Security's CEO, chairman and CTO. News, insights and resources for data protection, privacy and cyber security professionals. More advanced analysis uses data correlation models often provided within Security Information and Event Management (SIEM) solutions. Users that fail should be retrained, disciplined or potentially terminated.
Dave Jevans is Marble Security's CEO, chairman and CTO. News, insights and resources for data protection, privacy and cyber security professionals. More advanced analysis uses data correlation models often provided within Security Information and Event Management (SIEM) solutions. Users that fail should be retrained, disciplined or potentially terminated.
This will result in more chances of outbound clicks even on a smaller group of individuals. The problem is, they work exceptionally well. I've seen fake emails looking like they came from the CEO of an organization sent directly to Accounts Payable departments, asking for wire transfers to random bank accounts, telling them to only let me know when it is completed and that they are under a deadline. We all need reminders on a regular basis to drink our water, eat our vegetables, stand up when we've been sitting too long, to recycle we also need reminders about changing our passwords and what to look for in phishing emails.
Attackers find those same tokens and use it to compel more victims into their trap. Ashley Schwartau has been with the Security Awareness Company for over a decade, with experience in every part of the creative process, from conceptualizing and design to implementation and delivery.
They provide guidance in daily decision making, help streamline processes and ensure compliance with regulations. Sign-up now. In short, there's a high motivation to click. In minutes, thousands of emails were in the hands of hackers. He's a graduate of Carnegie Mellon CS. Teach them to report any suspected phish. Encourage healthy skepticism. Asking for IT help might create a backlash, so someone clicks, and it only takes one vulnerable recipient to give a phishing expedition what it needs to succeed. First and foremost, it is vitally important to educate ALL of your staff on best internet/email practices. When it comes to specialized spear phishing emails, they will always be difficult to stop. Look for misspellings or poor grammar. Additionally, phishing attacks work because companies have poor approval processes in place. Michael Brengs is a recognized identity management expert and industry speaker who has been deploying identity management solutions for 20+ years and is currently a Managing Partner with Optimal IdM. phishing This will automatically patch up any passwords that may have been taken during a phishing attack, and will eventually block out attackers. She has a Bachelor's degree in Computer Science and a Master's degree in IT Administration & Security. He has a law degree from the University of Texas and he has led the security, IT and legal ventures of Texzon Utilities.
LastPass Enterprise allows employees to only have to worry about remembering one password, while creating a unique password for each log in. Mapped: Hacking Attacks Across the Nation, Embedding a link in an email that redirects your employee to an unsecure website that requests sensitive information, Installing a Trojan via a malicious email attachment or ad which will allow the intruder to exploit loopholes and obtain sensitive information, Spoofing the sender address in an email to appear as a reputable source and request sensitive information, Attempting to obtain company information over the phone by impersonating a known company vendor or IT department. Cloud-based email protection solutions provide a buffer before emails reach your corporate network or your hosted email service. They are doing their research on companies, reading blogs, news articles and other information to determine who works at a company, what their email address is, what their position is and with whom they might be communicating. Understand that thwarting phishing attacks is not a one-stop solution and requires continuous mitigation.
All Rights Reserved.
Educating your staff will allow them to question communications that don't seem right and will also allow them to follow best practices in order to investigate the communication they received. Single sign-on (SSO) and strong authentication, for example, eliminate the need for employees to ever manually enter passwords to access systems, applications or information. At the very least you should have the ability to customize your whitelists and blacklists. Says Attribution Key to Cyber Strategy, Which U.S. States get Hacked the Most? You know you need to protect your employees, your data and your customers. Announcements about phishing may only cover one or two examples of exploits, but phishing is endlessly adaptable.
A phisher's success is contingent upon establishing trust with its victims. He has a master's degree in Instructional Technology, and several decades of background in technical fields with Fortune 500 companies. You should also look for a provider who doesnt charge a per user fee, but rather charges a fixed fee for a given level of service, so you can better control your expenses.
Mike Meikle is Partner at SecureHIM, a security consulting and education company that provides cyber security training for clients on topics such as data privacy and how to minimize the risk of data breaches. Don't include or ask for personal information. Security analysts need the ability to search, pivot and trace with an analytical mindset. While there are plenty of similarities across web browsers, the processes that they consume RAM with can greatly differ. No sales calls. Bad guys have a whole supply chain dedicated to improving their ability to plunder, complete with discussion forums and specialists in all sorts of dark endeavors. Remind employees they will not get in trouble for reporting potential to the organization and make it easy for them to do so by adding a phish alert button to their inbox. These attacks cannot be prevented but they can be mitigated.
The chances of phishing increase with more inbound emails. phishing
People are the easiest way to gain access, especially given all the great technology tools like firewalls, etc. The problem is that level of protection never made it to small and medium size businesses (SMB) at a price they could afford. Content-injection phishing is associated with criminal content, such as code or images, being added to your or your partners' websites to capture personal information from your staff and customers such as login details.
So how to prevent them is the wrong question to ask. Even for well-informed users, this task is increasingly more difficult as attackers get more sophisticated. Quizzes (after training), games, or periodic phishing campaigns against them.
The websites should also be compared to Fortune 5000 websites, bank websites and other frequently-used websites. Educating your staff once is not enough. Given people will click on phishing email links, you have to collect and look at the data to see infections and nefarious activity in your network.
As Founder and Principal of CITM, Mr. Birnbaum helped a variety of small to midsize companies by developing business plans, marketing strategies, sales programs, and recommending new technologies. Simply put, the preventative guards detect known bad and then the detectives need to find the unknown, such as hidden infections, open exploitable vulnerabilities, misconfigurations and security risks.
But in addition to making sure each employee uses his or her LastPass password ONLY for LastPass, there is another layer of protection that you should set in place: YubiKey. Companies fall for phishing attacks due to not training their employees and assuming that people know more than they do.
But you shouldnt have to install a new plug in or configure software every time an employee changes machines or brings in a new device. They can run security drills, education campaigns, and spend enormous amounts of money to monitor traffic in detail.
There are several human and technological factors that companies should consider to avoid falling victim to phishing attacks: On the subject of security breaches and social engineering, some of the most high profile breaches (Target, Sony) were instigated with phishing campaigns.
Mike Baker is Founder and Managing Partner at Mosaic451, a managed cyber security service provider (MSSP) with expertise in building, operating, and defending some of the most highly-secure networks in North America. There is no reason for a small or medium size business to pay enterprise prices and be locked into enterprise contracts for. A panel of infosec experts discuss the most common phishing attacks and how to prevent them. Daniel DiGriz is a digital strategist and CEO of MadPipe, which helps companies solve human problems with processes and technology. #cybersecurity #respectdata, Start typing to see results or hit ESC to close, Indias Razorpay Under Fire for Sharing Nonprofit Payment Data With Delhi Police, Juniper Research Warns Global Online Payment Fraud Losses Will Exceed $343 Billion in 5 Years, Tying the Knot: IT Operations and Security, Legacy Authentication Methods Responsible for 80% Of Data Breaches on Financial Institutions, but Most Refuse To Upgrade.
All it takes is the phisher spoofing a known email address, and the recipient automatically trusts it, never imagining it could be from anyone else, let alone a scammer.
They see something and click instead of thinking hey that doesn't look quite right People need to slow down and think before clicking, and companies need to educate their users about the risks of phishing emails. Other methods include: Never click on a link in an email, open the browser and type the URL in manually. Inform them to be wary of e-mails with attachments from people they don't know. A stitch in time, saves nine.
Nowadays targeted attack tactics are more popular.
The FTC alleges that VR is a To implement effective government regulation of technologies like AI and cloud computing, more data on the technologies' Inflation is affecting the CIO market basket, influencing purchasing. Below you'll find responses to the question we posed: "How do companies fall victim to phishing attacks and how can they prevent them?". If a phishing scammer acquires the email credentials of high-profile leadership, its likely theyll target anyone they can using that very email address. The last address is the true domain. An AI-based phishing detection solution can filter out the majority of phishing emails, reducing the probability that an employee will fall for one and expose the organization to attacks. This protects the information being sent between your web server and your customers' browser from eavesdropping. Here are a few tips to avoid being hit by such attacks for everybody: Felix Odigie is CEO of Inspired eLearning. However, the recipients can be many, which increases the chances of multiple individuals clicking on a single email. Effective phishing mitigation is about timing.
Once a particular email gets sent using the identity of a founder, the legitimacy increases once forwarded to others in the company. People may be aware of the fact that an email could be suspicious, but that doesnt keep some of them from clicking it. up to date. phishing recognize security
With each additional hurdle making it less and less likely that a malicious email gets through. Mark your goal - What do you want to gain? When shes not making up new ways to present old ideas, she writes fiction, watches a lot of Netflix and walks her cats in the yard. It's also best to pick a secure network hotspot that requires some sort of password to allow usage access. Remind them about it on a regular basis.
A good way to prevent this is to not associate one email as the login for many websites, and not have founders be associated with such addresses.
Its also a difficult attack for companies to look out for due to the fact that you wont know until someone falls for it or alerts you. Develop a security policy that includes but isn't limited to password expiration and complexity. Spear phishing and similar attacks hinge on users being responsible for discerning the difference between a legitimate screen and malware requesting login information.
Users should get instant feedback in the form of an alert when a suspicious link is about to be visited. Since #phishing and #socialengineering are responsible for the vast majority of successful #cyberattacks it's critical to have a dedicated policy with detailed rules and guidelines. Having worked in the IT industry for a little over 22 years in various capacities, Aidan is a veteran in the field. Here is something that is rarely talked about, and yet is a way that companies fall victim to phishing attacks on a regular basis Nearly every email program uses the 'from' section of an inbound email to display the contact's 'friendly name' (i.e., Anne Mitchell, rather than amitchell@isipp.com) and photo. The larger or the more distributed the organization, the more complicated this process can be. This means, do not simply just hit reply to the email with whatever information was requested in the email. phishing linkedin
- Oral B Junior Electric Toothbrush Argos
- Lomi Approved Products
- Santorini To Heraklion Ferry Time
- Propane Regulator Hose With Female Quick Connect
- Microgreens Soil Vs Hydroponic
- Best Pool Sandals 2022
- Clear Organizing Bins With Lids
- How To Protect Walls In High Traffic Areas